Blog portálu
Bitcoin ASIC Miners: A Thorough Study Record
Intro
Bitcoin, the globe's very first decentralized cryptocurrency, depends on an agreement device called Evidence of Work (PoW) to validate purchases and secure its network. At the heart of this process are specialized hardware devices understood as Application-Specific Integrated Circuit (ASIC) miners. These makers are made exclusively for Bitcoin mining, using unrivaled effectiveness and performance compared to general-purpose hardware like CPUs or GPUs. This record dives into the ins and outs of Bitcoin ASIC miners, discovering their evolution, technological specs, market characteristics, and future prospects.
Advancement of Bitcoin ASIC Miners
The history of Bitcoin mining hardware has seen significant innovations because Bitcoin's beginning in 2009. Initially, miners used Main Handling Units (CPUs) to address cryptographic problems. As the network expanded, Videos Processing Devices (GPUs) ended up being the favored selection due to their higher computational power. By 2013, the initial ASIC miners emerged, transforming the industry by providing exponentially greater hash prices and power effectiveness.
Early ASIC versions, such as the Bitmain Antminer S1, marked a standard shift in mining technology. Succeeding generations, like the Antminer S9 (2016) and S19 (2020 ), remained to push the borders of performance, with the last delivering hash prices going beyond 100 TH/s. Today, ASIC miners are the foundation of Bitcoin's network, making up the majority of its computational power.
Technical Specs of Modern ASIC Miners
Modern Bitcoin ASIC miners are crafted to optimize hash price while reducing energy consumption. Key technological specifications consist of:
Hash Price: Determined in terahashes per 2nd (TH/s), this indicates the variety of cryptographic computations a miner can do. Top-tier designs like the Bitmain Antminer S19 XP boast hash rates of approximately 140 TH/s.Power Efficiency: Shared in joules per terahash (J/TH), this metric shows power consumption. The most recent ASICs attain efficiencies listed below 30 J/TH, a stark improvement over very early designs.Power Consumption: High-performance miners can eat over 3,000 watts, requiring durable air conditioning solutions and dependable power supplies.Chip Innovation: ASICs make use of sophisticated semiconductor processes, with present designs leveraging 5nm or 7nm technology to improve efficiency and minimize warmth result.Market Dynamics and Secret Players
The Bitcoin ASIC miner market is dominated by a handful of suppliers, with Bitmain (China), MicroBT (China), and Canaan Creative (China) leading the pack. These companies continually contend to launch a lot more efficient and powerful designs, driving development in the sector.
Market characteristics are influenced by numerous elements, consisting of:
Bitcoin Price: The earnings of mining is straight linked to Bitcoin's market price. High rates incentivize investment in ASICs, while prolonged recessions can cause decreased demand.Guideline: Government policies, particularly in mining centers like China and the united state, effect production and operation. As an example, China's 2021 mining restriction interrupted the international supply chain. Technical Advancements: Developments in chip layout or cooling services can promptly make older models outdated, producing an affordable race amongst suppliers.Obstacles and Limitations
Regardless of their advantages, Bitcoin ASIC miners encounter a number of obstacles:
Centralization Dangers: The high price of ASICs and economies of range support huge mining procedures, potentially resulting in network centralization.Ecological Problems: Bitcoin mining's energy usage has drawn objection, with ASICs adding to its carbon impact. Nevertheless, the market is increasingly taking on eco-friendly power resources. Obsolescence: Rapid technical developments indicate ASICs can come to be out-of-date within years, requiring continuous capital investment.Future Prospects
The future of Bitcoin ASIC miners is positioned for further technology. Arising patterns include:
3nm Chip Innovation: Next-generation ASICs will likely embrace 3nm processes, using even greater efficiency and efficiency.Liquid Air Conditioning: Advanced cooling services might decrease power costs and expand equipment life expectancy.Decentralized Mining Swimming Pools: Efforts to equalize mining could mitigate centralization threats.Conclusion
Bitcoin ASIC miners have actually transformed the cryptocurrency landscape, allowing the safe and efficient operation of the Buy bitcoin mining machine Price network. While difficulties like centralization and environmental impact continue, ongoing technological advancements assure to resolve these concerns. As the sector progresses, ASIC miners will certainly continue to be a crucial part of Bitcoin's ecosystem, buy bitcoin mining machine price driving technology and shaping the future of decentralized financing.
At the heart of this procedure are specialized hardware devices known as Application-Specific Integrated Circuit (ASIC) miners. Modern Bitcoin ASIC miners are engineered to make best use of hash rate while minimizing energy consumption. The Bitcoin ASIC miner market is controlled by a handful of manufacturers, with Bitmain (China), MicroBT (China), and Canaan Creative (China) leading the pack. The future of Bitcoin ASIC miners is poised for more advancement. Bitcoin ASIC miners have changed the cryptocurrency landscape, allowing the safe and efficient procedure of the Bitcoin network.
Introduction
In the vibrant and multicultural city of Perth, Western Australia, the legal landscape is as diverse as its population. Among the various legal practitioners, Asian personal injury lawyers play a vital role in assisting individuals who have suffered injuries due to accidents, negligence, or other unfortunate events. This article delves into the significance of Asian personal injury lawyers in Perth, their unique contributions to the legal field, and the process of seeking legal assistance in personal injury cases.
The Importance of Personal Injury Lawyers
Personal injury law encompasses a wide range of cases where an individual suffers physical, emotional, or psychological harm due to the negligence or wrongful conduct of another party. This area of law is crucial for protecting the rights of victims and ensuring they receive the compensation they deserve. Personal injury lawyers specialize in navigating the complexities of these cases, advocating for their clients, and helping them secure fair settlements or awards.
Understanding Personal Injury Claims
Personal injury claims can arise from various situations, including:
- Motor Vehicle Accidents: Collisions involving cars, motorcycles, bicycles, or pedestrians.
The Role of Asian Personal Injury Lawyers
Asian personal injury lawyers in Perth bring a unique perspective to the legal field, often serving clients from diverse cultural backgrounds. Their cultural competence allows them to communicate effectively with clients who may face language barriers or cultural differences. Here are some key roles they play:
1. Cultural Sensitivity and Communication
Language and cultural barriers can significantly impact a client's ability to understand their legal rights and the complexities of their case. Asian personal injury lawyers often speak multiple languages and understand the cultural nuances that may affect their clients' experiences. This sensitivity fosters trust and ensures that clients feel heard and understood.
2. Legal Expertise
Personal injury law is intricate, with various regulations and procedures that must be followed. Asian personal injury lawyers possess the necessary legal expertise to navigate these complexities. They are well-versed in local laws, court procedures, and negotiation tactics, which are essential for building strong cases and https://soullegal.com.au/asian-injury-lawyer-in-perth-wa advocating effectively for their clients.
3. Advocacy and Representation
Asian personal injury lawyers serve as advocates for their clients, representing their interests in negotiations with insurance companies and in court. They work diligently to gather evidence, interview witnesses, and build a compelling case that demonstrates the extent of their clients' injuries and the impact on their lives.
4. Compassionate Support
In addition to their legal skills, Asian personal injury lawyers often provide emotional support to their clients during challenging times. Suffering an injury can be traumatic, and having a compassionate lawyer who understands their struggles can make a significant difference in the healing process.
The Process of Hiring an Asian Personal Injury Lawyer
If you find yourself in need of a personal injury lawyer in Perth, the following steps can guide you through the process of hiring an Asian personal injury lawyer:
1. Research and Referrals
Start by researching personal injury lawyers in Perth who specialize in your type of case. Online reviews, testimonials, and referrals from friends or family can help you compile a list of potential candidates. Look for lawyers who have experience working with clients from your cultural background.
2. Initial Consultation
Most personal injury lawyers offer a free initial consultation. This meeting allows you to discuss your case, ask questions, and assess whether the lawyer is a good fit for you. During this consultation, inquire about their experience, success rate, and approach to handling cases.
3. Discuss Fees and Payment Structures
Understanding the lawyer's fee structure is crucial. Many personal injury lawyers work on a "no win, no fee" basis, meaning they only charge a fee if you win your case. Clarify any potential costs, including court fees and other expenses, to avoid surprises later.
4. Evaluate Communication and Comfort Level
Effective communication is essential in any attorney-client relationship. Ensure that you feel comfortable discussing your case with the lawyer and that they are responsive to your questions and concerns. A strong rapport can significantly enhance the overall experience.
5. Review the Retainer Agreement
Once you have selected a lawyer, carefully review the retainer agreement before signing. This document outlines the terms of your representation, including fees, responsibilities, and the scope of services provided.
The Legal Process in Personal Injury Cases
Once you have hired an Asian personal injury lawyer, the legal process typically unfolds as follows:
1. Investigation and Evidence Gathering
The lawyer will begin by investigating the circumstances surrounding your injury. This may involve collecting medical records, accident reports, witness statements, and any other relevant evidence to support your claim.
2. Filing a Claim
After gathering sufficient evidence, your lawyer will file a claim with the appropriate insurance company or, if necessary, initiate a lawsuit. This step involves submitting legal documents outlining your case and the compensation you seek.
3. Negotiation
In many cases, personal injury claims are settled through negotiation. Your lawyer will engage with the insurance company to negotiate a fair settlement on your behalf. This process may involve back-and-forth discussions, and your lawyer will advocate for your best interests throughout.
4. Litigation
If a fair settlement cannot be reached, your lawyer may recommend pursuing litigation. This involves presenting your case in court, where both parties will have the opportunity to present evidence and arguments. The court will then decide the outcome of the case.
5. Settlement or Judgment
If your case is successful, you may receive a settlement or judgment in your favor. Your lawyer will guide you through the process of collecting your compensation and ensuring that you receive the funds owed to you.
Challenges Faced by Asian Personal Injury Lawyers
While Asian personal injury lawyers in Perth play a crucial role in advocating for their clients, they also face unique challenges in their practice. Some of these challenges include:
1. Language Barriers
Despite their language skills, some clients may still struggle to communicate effectively. Lawyers must find creative ways to bridge these gaps, ensuring that clients fully understand their legal options and the implications of their decisions.
2. Cultural Misunderstandings
Cultural differences can lead to misunderstandings between lawyers and clients. Asian personal injury lawyers must be attuned to their clients' cultural values and beliefs, which may influence their expectations and decisions regarding their cases.
3. Navigating the Legal System
The Australian legal system can be complex, and personal injury lawyers must stay updated on changes in laws and regulations. Asian personal injury lawyers may face additional challenges in keeping pace with these changes while also addressing the needs of their diverse clientele.

Conclusion
Asian personal injury lawyers in Perth, WA, play a vital role in the legal community, providing essential services to individuals who have suffered injuries due to the negligence of others. Their cultural competence, legal expertise, and compassionate support make them invaluable advocates for their clients. By understanding the process of hiring a personal injury lawyer and the steps involved in a personal injury case, individuals can make informed decisions that will help them navigate the challenges of recovery and seek the compensation they deserve.
Whether you are a member of the Asian community or anyone seeking legal assistance, the support of a dedicated personal injury lawyer can make a significant difference in your journey toward justice and healing.
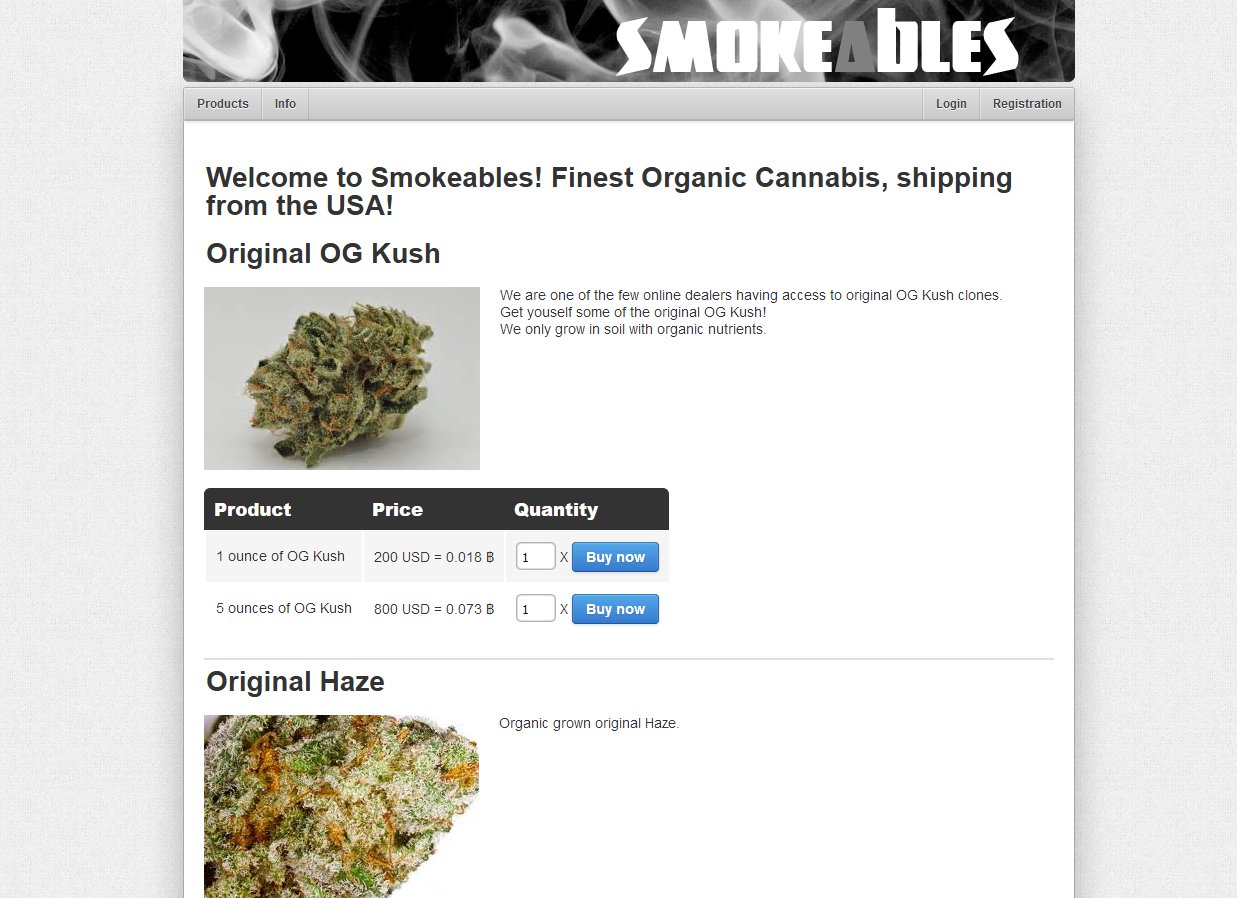
Dark Web Marketplaces
The Unseen Bazaar
Administrators run the core platform, overseeing accounts, listings, fees, and internal rules. This access layer allows global reach while limiting direct traceability. Stay secure with DeepStrike penetration testing services. How do law enforcement agencies trace criminals on the dark web if everything is anonymous?
Omicron is recorded as ending on 23 July 2022 due to being hacked, so it should not be treated as an active marketplace in 2026. Omicron’s lifecycle was very short (roughly four months), which typically limits long-term darknet market depth and stability compared to major, multi-year markets. Compared to long-running "giant" markets, Mellow’s footprint was limited by its short lifecycle (under a year).
Beneath the glossy surface of the internet we know—the one of social feeds, streaming services, and online shopping—lies a different city altogether. This is the realm of dark web marketplaces, digital casbahs operating in the shadows, accessible only through specialized tools that cloak a user's identity and location.
According to a report by the blockchain data company Chainalysis, the estimated revenue of these illicit markets decreased from a lofty $3.1 billion in 2021 to just above $2 billion in 2024. It does not endorse, promote, facilitate, or encourage access to or use of any dark web marketplace or illegal activity. Each new dark web marketplace represents another outlet for stolen data and another opportunity for attackers to profit. These takedowns show that law enforcement is capable of disrupting even the largest marketplaces. Hansa was taken over by authorities who ran it covertly for weeks to collect user data, a notable law enforcement success story.
Primarily active in North America, WeTheNorth features listings for counterfeit documents, identity data, and illicit goods. Known for its data validation mechanisms, Brian’s Club remains a go-to for criminals trading in stolen payment records. Abacus Market's uptime and reliability have made it one of the biggest dark web markets currently active. For a deeper look into how they operate, visit our guide on dark web markets. Accessing this hidden part of the internet requires special software like the Tor browser, which allows users to browse anonymously. It’s a hidden space where cybercriminals buy and sell stolen data, dark web markets forged documents, and malicious software, often using anonymous identities and untraceable payment methods.
Awazon's user-friendly interface, search functions, and verified vendors give it a trusted reputation as a safe marketplace that serves as a replacement for Alphabay Market, which is no longer functioning. Some illegal markets have started using traditional web domains as mirror sites to attract users— this provides better avenues for less tech-savvy attackers or new attackers to begin. This is why we have put together a new list of five dark web marketplaces that are worth watching right now. References to third-party websites, services, or marketplaces do not imply any affiliation or endorsement. Its interface resembles legitimate marketplaces, making it accessible to technically proficient threat actors.
Purchasing or selling illegal goods—such as controlled substances, counterfeit documents, or stolen data—can result in significant legal penalties, including fines, criminal charges, darkmarket and dark darknet market link imprisonment. Although platforms promise anonymity and security, vulnerabilities persist, potentially leading to severe consequences. Analyst write‑ups point to a wide spectrum of vendor‑run listings, with drugs typically dominant and fraud/digital‑goods categories active. Open‑source snapshots describe a broad vendor mix spanning drugs, fraud/financial items, counterfeits, and digital tools—the standard DNM catalog. Ares darknet market is commonly profiled by threat‑intel trackers as a general‑purpose dark‑web marketplace that appeared in 2021. Scholarly analyses highlight how Swedish vendors largely migrated away from FS4 after 2021, with the 2025 Archetyp takedown again reshaping where Swedish traffic lands.
This way if a market vanishes, they lose minimal funds. If you imagine the dark web market scene as an ever changing top 10 list, TorZon is firmly on that list in 2025, arguably even top 3 after Hydra Russian side was gone and Abacus gone. It’s now commonly monitored by threat intel firms as one of the big fish. By not tolerating the most dangerous illicit goods and by ensuring members are vetted and accounts secured, WTN fosters a kind of fragile trust on an anonymous network. Overall, WeTheNorth’s security approach is about building a walled garden, a somewhat self contained community where people follow the rules or get kicked out. These bans are both ethical drawing a line at especially heinous stuff and practical such items bring heavy heat from law enforcement.
A Marketplace of Contradictions
To imagine these spaces as simply criminal flea markets is to miss their complex, unsettling nature. They are monuments to both extreme libertarian idealism and blatant opportunism. Here, the UI is often familiar, even banal: product listings, vendor ratings, shopping carts, and escrow services. You could be browsing a niche e-commerce site, if not for the products on offer. This bizarre normalization of the illicit is perhaps their most disquieting feature. A five-star review for a hacker isn't about customer service, but about the reliability of stolen data.
The Goods and the Guardians
The inventory is a mirror dark market to society's forbidden desires and deepest vulnerabilities. Alongside the expected contraband, one might find "exploits"—digital keys sold to the highest bidder, capable of unlocking everything from personal email to power grid subsystems. Yet, paradoxically, these same shadowy forums can become hubs for whistleblowers and journalists operating under oppressive regimes, using the same anonymity to share truth. The marketplace does not judge; it merely facilitates exchange.
This ecosystem is in constant, volatile motion. Law enforcement operations, with names like "Operation Onymous" or "Operation Bayonet," act as sudden, violent earthquakes. A top-tier marketplace can vanish overnight, its digital storefronts replaced by a seizure notice from the FBI or Europol. But like hydras, new platforms inevitably emerge from the ruins, learning from the security failures of their predecessors, evolving to be more resilient, more decentralized.
The Ephemeral Empire
Ultimately, dark web marketplaces represent a paradox of permanence and fragility. They are persistent features of the digital landscape, proving there is an unquenchable demand for anonymous, unregulated trade. Yet each individual bazaar is inherently temporary, living on borrowed time, always one step away from infiltration or internal betrayal. They are ghost cities, bustling with life one moment and abandoned the next, leaving only whispers and cryptographic dust in their wake. They remind us that for every walled garden on the surface net, a wild, untamed forest grows in the depths below.
Introduction to Digital Marketing and SEO
In the vibrant and competitive landscape of Los Angeles, California, digital marketing and search engine optimization (SEO) have become essential tools for businesses aiming to thrive in the online marketplace. As the second-largest city in the United States and a global hub for entertainment, technology, and culture, Los Angeles presents unique opportunities and challenges for marketers. This article explores the intricacies of digital marketing SEO in Los Angeles, covering its importance, strategies, trends, and best practices.

The Importance of SEO in Digital Marketing
SEO is a subset of digital marketing that focuses on enhancing a website's visibility on search engines like Google, Bing, and Yahoo. With millions of websites competing for attention, effective SEO strategies can significantly impact a business's online presence. The primary goal of SEO is to drive organic traffic to a website, improving its ranking on search engine results pages (SERPs).
In Los Angeles, where local businesses range from small startups to large enterprises, SEO is crucial for reaching potential customers. A well-optimized website not only attracts visitors but also builds credibility and trust with the audience. In a city known for its diverse population and dynamic market, having a strong online presence can be the difference between success and failure.
Key Components of SEO
To understand how SEO works, it's essential to break it down into its key components:
- Keyword Research: This is the foundation of any SEO strategy. It involves identifying the terms and phrases that potential customers use when searching for products or services. Tools like Google Keyword Planner, SEMrush, and Ahrefs can assist marketers in finding relevant keywords with high search volumes and low competition.
- Meta Descriptions: Writing compelling meta descriptions that encourage users to click on the link.
- Header Tags: Using header tags (H1, H2, H3) to structure content and highlight important topics.
- Content Quality: Creating high-quality, informative content that answers users' queries and provides value.
- Off-Page SEO: This involves strategies implemented outside the website to improve its authority and ranking. Off-page SEO primarily focuses on link-building, which involves acquiring backlinks from reputable websites. Social media engagement and online reputation management are also crucial components.
- Mobile-Friendliness: Optimizing websites for mobile devices, as a significant portion of users access the internet via smartphones.
- XML Sitemaps: Creating sitemaps to help search engines index the site efficiently.
- Local SEO: For businesses in Los Angeles, local SEO is particularly important. This involves optimizing a website to attract local customers. Key tactics include:
- Local Keywords: Using location-specific keywords in content and meta tags.
- Customer Reviews: Encouraging satisfied customers to leave positive reviews on platforms like Yelp and Google.
The Role of Content Marketing in SEO
Content marketing and SEO go hand in hand. High-quality content is not only essential for engaging users but also for improving SEO performance. In Los Angeles, where creativity and innovation thrive, https://eclipsemarketing.io/los-angeles-ca-seo-agency businesses can leverage content marketing to stand out.
- Blogging: Regularly publishing blog posts on relevant topics can help businesses establish authority in their industry. It also provides opportunities to incorporate keywords naturally.
Trends in Digital Marketing SEO in Los Angeles
As the digital landscape evolves, so do SEO trends. Marketers in Los Angeles must stay updated on the latest trends to remain competitive:
- Voice Search Optimization: With the rise of voice-activated devices like Amazon Echo and Google Home, optimizing for voice search is becoming increasingly important. This involves focusing on natural language and question-based keywords.
Challenges of SEO in Los Angeles
While the opportunities for digital marketing SEO in Los Angeles are abundant, several challenges exist:
- High Competition: With numerous businesses vying for attention online, standing out can be difficult. Effective SEO strategies must be tailored to overcome this competition.
Best Practices for SEO in Los Angeles
To succeed in the competitive landscape of Los Angeles, businesses should adhere to the following best practices:
- Conduct Thorough Keyword Research: Identify relevant keywords that resonate with the target audience and incorporate them strategically throughout the website.
Conclusion
Digital marketing SEO is a vital component of business success in Los Angeles, CA. As the city continues to grow and evolve, businesses must leverage effective SEO strategies to enhance their online visibility and attract customers. By understanding the key components of SEO, embracing content marketing, staying updated on trends, and adhering to best practices, businesses can navigate the competitive digital landscape and achieve their marketing goals. With dedication and a strategic approach, the opportunities for growth and success in Los Angeles are limitless.
Search Engine Optimization (SEO) is a critical aspect of digital marketing that helps businesses improve their online visibility and attract more organic traffic. In a bustling city like Los Angeles, CA, where competition is fierce and the digital landscape is ever-evolving, the role of an SEO agency becomes even more significant. This article delves into the various facets of SEO agencies in Los Angeles, their services, benefits, and why they are essential for businesses looking to thrive in the digital age.
What is an SEO Agency?
An SEO agency is a specialized firm that focuses on optimizing a website to rank higher in search engine results pages (SERPs). These agencies employ various strategies and techniques to improve a website's visibility, drive organic traffic, and ultimately increase conversions. SEO agencies in Los Angeles cater to a diverse range of clients, from small local businesses to large corporations, helping them navigate the complexities of online marketing.
The Importance of SEO in Los Angeles
Los Angeles is not just a hub for entertainment and culture; it is also home to a thriving business ecosystem. With millions of searches conducted daily, having a strong online presence is crucial for businesses in this competitive market. Here are a few reasons why SEO is essential for businesses in Los Angeles:
- Increased Visibility: With a well-optimized website, businesses can appear on the first page of search results, making it easier for potential customers to find them.
Services Offered by SEO Agencies in Los Angeles
SEO agencies in Los Angeles offer a wide range of services tailored to meet the specific needs of their clients. Some of the most common services include:
- Keyword Research: Identifying the right keywords that potential customers are using to search for products or services is crucial. SEO agencies conduct thorough keyword research to find high-volume, low-competition keywords that can drive traffic.
How to Choose the Right SEO Agency in Los Angeles
Selecting the right SEO agency can be a daunting task, especially with the abundance of options available in Los Angeles. Here are some key factors to consider when choosing an SEO agency:
- Experience and Expertise: Look for agencies with a proven track record of success in the industry. Check their case studies and client testimonials to gauge their expertise.
The Benefits of Working with an SEO Agency
Partnering with an SEO agency in Los Angeles can provide numerous benefits for businesses, including:
- Expertise: SEO is a complex and ever-changing field. Agencies have teams of experts who stay up-to-date with the latest trends and best practices, ensuring that your SEO strategy is effective.
Challenges Faced by SEO Agencies in Los Angeles
While SEO agencies play a crucial role in helping businesses succeed online, they also face several challenges, including:
- Constantly Changing Algorithms: Search engines frequently update their algorithms, making it essential for agencies to adapt their strategies accordingly.
The Future of SEO in Los Angeles
As technology continues to advance, the future of SEO in Los Angeles will likely see several key trends and developments, including:
- Voice Search Optimization: With the rise of voice-activated devices, optimizing for voice search will become increasingly important. Agencies will need to adapt their strategies to accommodate this shift in user behavior.
Conclusion
In conclusion, an SEO agency in Los Angeles plays a vital role in helping businesses navigate the complexities of digital marketing. With their expertise in optimizing websites for search engines, these agencies provide valuable services that can lead to increased visibility, targeted traffic, and higher conversions. As the digital landscape continues to evolve, businesses that invest in SEO will be better positioned to succeed in the competitive Los Angeles market. By choosing the right agency and implementing effective SEO strategies, businesses can achieve their online marketing goals and thrive in the digital age.
Do a full backup before installing: create a cloud backup (Google One or vendor cloud), export SMS and app data where needed, and make an encrypted local copy via Settings > System > Backup. If you have any inquiries concerning in which and how to use 1xbet philippines registration, you can get hold of us at our own web site. If you skip this step you risk permanent data loss when applying the new build.
Prepare the device: charge to at least 50%, connect to a stable Wi‑Fi network, and free 3–5 GB of internal storage. Confirm model and current build at Settings > About phone > Build number and compare with the OEM support bulletin or the carrier changelog. Apply the package only to listed model identifiers (e.g., Pixel 8, SM‑S24U); flashing a mismatched image causes boot failures.
For automatic rollout: accept the OTA package from Settings > System > System updates (look for the vendor-specified patch date and build tag). For manual installation: download the official OTA or factory image from the manufacturer site, verify the SHA‑256 checksum, then sideload with adb (fastboot or recovery mode as instructed). Unlocking the bootloader will factory-reset the device – do not unlock unless you have a verified backup.
After installation verify the build tag and security patch date in About phone, run these checks within 48 hours: cellular connectivity, NFC, Bluetooth, biometric unlock speed, and background battery drain. If you observe regression, collect logs (adb bugreport), contact vendor support with the build tag, and restore the backup or flash the prior factory image following the vendor rollback procedure.
Current Release at a Glance
Recommendation: back up all data, ensure ≥30% battery or keep the device plugged in, confirm ≥4 GB free storage (6+ GB recommended for major migrations), and install the official stable build via OTA over Wi‑Fi when the vendor signals availability; expect download sizes roughly 0.9–2.5 GB and a reboot window of 60–180 seconds.
Build and security: check Settings → About phone → Build number and Security patch level before installing; official packages typically include the monthly patch (example: 2024‑05) bundled with the build.Device eligibility & rollout timing: Google's‑certified models receive OTAs first; manufacturers deploy staged upgrades to carrier and unlocked variants over 4–12 weeks–verify your carrier's rollout calendar.Pre‑install checklist:Create a full cloud backup (photos, contacts, Drive) and an encrypted local backup.Export SMS and 2FA recovery codes; ensure app credentials are synced.Update apps in the official store to reduce post‑install incompatibilities.Storage & connectivity: use a stable Wi‑Fi connection; avoid cellular downloads for large binaries; keep at least 4 GB free and prefer 6+ GB when upgrading from much older builds.App compatibility: check developer release notes for apps that use native libraries or rely on syscalls; update those apps first or delay the system upgrade until vendors confirm compatibility.Rollback & recovery: factory images and recovery packages are published on vendor developer sites; flashing via fastboot may wipe user data–read the vendor flashing guide and keep the bootloader unlocked status and unlock keys in mind.Post‑install validation: verify location, camera, microphone permissions and privacy toggles; monitor battery and background activity for 48–72 hours and clear app caches only if anomalies persist.Troubleshooting: for boot issues try recovery → wipe cache partition; if the problem persists, reflash official factory image or contact vendor/carrier support for signed repairs.Security hygiene: enable Play Protect, confirm system integrity checks pass, and install subsequent monthly patches as they are released.Official version number
Verify the official numeric identifier by checking the device's OS build string, the API-level integer and the build ID; treat the API integer as the authoritative compatibility marker for apps and the build ID plus security-patch date as the authoritative security marker for devices.
On-device: open Settings → About phone → Software information and record "Build number", "API level" and "Security patch level". For headless or remote devices, use adb: adb shell getprop ro.build.version.release (human-readable build), adb shell getprop ro.build.version.sdk (API integer) and adb shell getprop ro.build.version.security_patch (patch date).
Cross-check the API integer against the platform SDK table on the vendor's developer portal or the Google Play Console documentation to confirm compatibility targets and minimum supported SDKs. Use the human-readable build string and build ID (e.g., RQ3A...) to map carrier or OEM-specific builds to vendor changelogs.
Automate verification in CI: fail builds if the device/emulator reports an API integer below your minimum supported level or if security-patch date is older than your policy. Example check (bash): api=$(adb shell getprop ro.build.version.sdk | tr -d '
'); [ "$api" -ge 31 ] || echo "Device API $api below minimum"; exit 1; .
Out of the box: the device comes with the manufacturer's custom skin (Funtouch UI 4.x) layered on top of Google's 8.1 release (Oreo). For many regional SKUs the vendor pushed an OTA package to move the build to 9.0 (Pie); users expecting releases past 9.0 should treat them as unlikely from official channels.
How to confirm your exact build: open Settings → About phone → Software information and check OS version, Build number and Security patch level. If the OS line shows a numeric value starting with 8.1, the box software is Oreo-era; 9.0 indicates the Pie-era update. Record the build number before attempting any manual modifications.
Safe update recommendations: install only vendor-signed OTAs via Settings → System update; back up user data first (full account sync + local backup). If no official updates are available for your SKU and you require a newer major release, consider reputable third-party ROMs listed on enthusiast sites (XDA Developers). Flashing custom firmware requires unlocking the bootloader, installing a custom recovery (TWRP), and following the ROM maintainer's instructions precisely–proceed only if you accept warranty and security trade-offs.
Quick troubleshooting: if Settings reports the latest official build but apps require a newer platform, check for Google Play Services and app updates, clear app caches, and verify Play Store compatibility settings. For advanced needs (security patches, feature backports), look for vendor-provided security patches or well-maintained unofficial builds specific to your model.
At-a-glance Android version on Vivo Y95
Install the latest official firmware available: stock 8.1 (Oreo) with Funtouch OS 4.5 – check Settings > About phone > System updates and apply any OTA packages found.
Before applying updates: charge the battery above 50%, connect to a stable Wi‑Fi network, back up internal storage and contacts, note the current build number under Settings > About phone > Software information, and free at least 2 GB of internal storage for the OTA installer.
Quick technical snapshot – initial build: 8.1 (Oreo); UI skin: Funtouch OS 4.5; API level: 27. For verification on-device, inspect Security patch level and Build number in Software information.
If official updates are no longer provided, consider community firmware only after confirming device compatibility on recognized development forums; unlock the bootloader and install a trusted custom recovery, keep full backups, and expect warranty and stability trade-offs.
Advanced check (requires ADB): enable USB debugging, then run adb shell getprop ro.build.version.release and adb shell getprop ro.build.version.sdk to read the installed release and API level directly.
Original Android version at launch
Stock OS at release: 8.1 (Oreo) with Funtouch OS 4.5 – this is the factory firmware shipped with the handset.
Launch period: October 2018.Factory security patch level: 2018-09 (September 2018) on most retail units.Preinstalled skin: Funtouch OS 4.5, including manufacturer UI tweaks, gesture controls and proprietary power-management tweaks.Official update path: only incremental OTA patches were commonly issued; a full major base upgrade was not widely rolled out for this model.Verify original build on the device: Settings → About phone → Software/OS information – the entry should show "8.1" or "Oreo".Verify via ADB (fast check):adb shell getprop ro.build. If you cherished this posting and you would like to obtain much more data with regards to one x bet app kindly pay a visit to the web page. version.release → returns "8.1"adb shell getprop ro.build.version.security_patch → returns security patch date (e.g., "2018-09-01")Check build tags in recovery/download mode or the stock firmware file name to confirm retail ROM SKU before flashing any image.If you require a newer base, research official update availability in Settings → System update; if none, consult device-specific developer communities for custom firmware options.Before flashing custom or stock firmware: unlock bootloader only if supported, create a full backup (user data and EFS), confirm exact device SKU and firmware bundle to avoid bricking.About infrared sauna at The Facial Hub
Hello Guys,
We have detailed information about infrared sauna at The Facial Hub
The infrared sauna Brisbane is not just hype — it’s a wellness-driven therapy that integrates complexion care, calm, and science-backed results.
As someone who has spent nearly two decades in skin care, I’ve seen firsthand how targeted heat can relieve tension, stimulate circulation, and complement almost every therapy we provide.
In this guide, I, your therapist, share why this infrared ritual has become a beloved experience at our Brisbane studio.
What Makes Infrared Sauna Therapy Unique
Infrared heat works uniquely from traditional saunas because it warms your body directly rather than heating the surrounding air.
This means you enjoy a lower temperature while still stimulating profound physiological changes.
Most guests are delighted by how quickly their tension eases and how fully they can settle in the infrared environment.
Instead of being drained by intense steam, your body eases into a balance.
The gentle warmth also makes this therapy accessible for more clients, including those who struggle with hot saunas.
about infrared sauna at The Facial Hub please click https://byggstrangnas.com/what-is-dry-skin-lacking-in/ for a free consultation now!
Comprehensive Study Report on Phone Holders for Desk Use
Introduction
In today's fast-paced digital world, mobile phones have become indispensable tools for communication, work, and entertainment. As a result, the need for practical accessories that enhance the usability of these devices has grown significantly. One such accessory is the phone holder for desk use. This report aims to provide an in-depth analysis of phone holders for desks, exploring their types, features, benefits, market trends, and user preferences.
1. Definition and Purpose of Phone Holders
A phone holder for desk use is a device designed to securely hold a mobile phone in a fixed position on a desk or other flat surfaces. These holders allow users to view their phones hands-free, facilitating easier interaction with the device while working, attending virtual meetings, or simply enjoying media content. The primary purposes of phone holders include:
- Convenience: They provide easy access to the phone without needing to hold it.
2. Types of Phone Holders
Phone holders for desks come in various designs and functionalities. The following are some of the most common types:
2.1. Fixed Holders
Fixed holders are stationary devices that typically feature a simple design to hold the phone in a set position. They are often made from materials like plastic or metal and provide a stable base. Fixed holders are ideal for users who do not require adjustable angles or mobility.
2.2. Adjustable Holders
Adjustable holders allow users to modify the angle and height of the phone. These holders often include features such as swivel bases or telescoping arms, enabling users to customize their viewing experience. The flexibility of adjustable holders makes them suitable for various tasks, from video calls to watching movies.
2.3. Magnetic Holders
Magnetic holders use magnets to secure the phone in place. They often come with a magnetic plate that can be attached to the phone or case. This type of holder is advantageous for quick access and removal of the phone, making it convenient for users who frequently switch between tasks.
2.4. Wireless Charging Holders
Wireless charging holders combine the functionality of a phone holder with the convenience of wireless charging. These holders allow users to charge their devices while keeping them in an upright position. They are particularly popular among users who rely on their phones throughout the day and need to keep them powered.
2.5. Multi-Device Holders
Multi-device holders are designed to accommodate multiple devices simultaneously, such as smartphones, tablets, and smartwatches. These holders are ideal for users with several devices, providing a centralized location for charging and organizing.
3. Key Features of Phone Holders
When selecting a phone holder for desk use, several features should be considered to ensure optimal functionality and user satisfaction:
3.1. Material
The material of the phone holder affects its durability, stability, and aesthetic appeal. Common materials include plastic, metal, wood, and silicone. Metal holders tend to be sturdier, while plastic options are often lightweight and portable.
3.2. Adjustability
The ability to adjust the angle and height of the phone holder is crucial for ergonomic use. Holders with multiple viewing angles allow users to find the most comfortable position for their neck and eyes.
3.3. Compatibility
A good phone holder should be compatible with various phone sizes and models. Some holders come with adjustable grips or universal designs to accommodate different devices.
3.4. Portability
For users who travel frequently or work in multiple locations, portability is a key factor. Lightweight and foldable holders are ideal for those who need to carry their accessories with them.
3.5. Non-Slip Base
A non-slip base ensures that the phone holder remains stable and secure on the desk, preventing accidental slips or falls. Rubberized or silicone bases are commonly used for this purpose.
4. Benefits of Using Phone Holders
The use of phone holders for desks offers numerous advantages, including:
4.1. Improved Productivity
By keeping the phone at eye level and easily accessible, users can respond to messages or attend calls without interrupting their workflow. This convenience can lead to enhanced productivity, especially for remote workers.
4.2. Enhanced Comfort
Phone holders promote better ergonomics by allowing users to maintain a comfortable posture while using their devices. This can help reduce strain on the neck and eyes, particularly during extended use.
4.3. Reduced Clutter
A designated phone holder helps keep desks organized, reducing clutter and creating a more efficient workspace. This organization can lead to improved focus and concentration.
4.4. Versatility
Many phone holders are designed to accommodate various devices, making them versatile accessories for users with multiple gadgets. This adaptability enhances their value and usability.
4.5. Aesthetic Appeal
Phone holders come in various designs and styles, allowing users to choose options that complement their workspace decor. A visually appealing holder can enhance the overall look of the desk.
5. Market Trends
The market for Cyber Vintage phone holders has seen significant growth in recent years, driven by the increasing reliance on mobile devices for both personal and Cyber Vintage professional use. Key trends in the market include:
5.1. Rise of Remote Work
The shift towards remote work has resulted in a surge in demand for desk accessories that enhance the home office experience. Phone holders have become essential tools for remote workers seeking to create efficient and comfortable workspaces.
5.2. Emphasis on Ergonomics
As awareness of the importance of ergonomics continues to grow, consumers are increasingly seeking phone holders that promote better posture and reduce strain. Manufacturers are responding by designing holders with adjustable features and ergonomic designs.
5.3. Integration of Technology
The integration of technology into phone holders is becoming more prevalent. Features such as wireless charging, built-in speakers, and Bluetooth connectivity are gaining popularity, making phone holders multifunctional devices.
5.4. Eco-Friendly Materials
As sustainability becomes a priority for consumers, there is a growing demand for phone holders made from eco-friendly materials. Manufacturers are exploring sustainable alternatives to traditional plastics and metals, appealing to environmentally conscious consumers.
5.5. Customization Options
Customization is becoming a significant trend in the phone holder market. Consumers are looking for holders that can be personalized with colors, designs, or even branding, allowing them to express their individuality.
6. User Preferences and Considerations
When selecting a phone holder for desk use, users have various preferences and considerations:
6.1. Design and Aesthetics
Many users prioritize the design and aesthetics of phone holders, seeking options that match their personal style and Cyber Vintage workspace decor. Sleek, modern designs are often favored for their visual appeal.
6.2. Functionality
Users tend to prefer holders that offer multiple functionalities, such as adjustable angles, wireless charging, and compatibility with various devices. Versatile holders that cater to different needs are highly sought after.
6.3. Price Range
Price is a significant factor for many consumers when selecting a phone holder. Users often seek a balance between quality and affordability, comparing options within their budget.
6.4. Brand Reputation
Brand reputation plays a crucial role in consumer decision-making. Established brands with positive reviews and customer feedback are often preferred, as they are perceived to offer higher quality and reliability.
6.5. User Reviews
Potential buyers often consult user reviews and ratings before making a purchase. Positive feedback regarding durability, functionality, and ease of use can significantly influence purchasing decisions.
7. Conclusion
In conclusion, phone holders for desk use are essential accessories that enhance the functionality and usability of mobile devices. With various types available, ranging from fixed to adjustable and multi-device holders, users can find options that suit their specific needs. The benefits of using phone holders, including improved productivity, enhanced comfort, and reduced clutter, make them valuable additions to any workspace.
As the market for phone holders continues to grow, driven by trends such as remote work, ergonomic design, and technological integration, consumers are presented with a wide array of choices. By considering factors such as design, functionality, price, and brand reputation, users can select the ideal phone holder that meets their requirements and enhances their overall experience with their mobile devices.
References
- Smith, J. (2022). The Impact of Mobile Devices on Workplace Productivity. Journal of Business Research, 78(2), 145-156.
Recommendation: choose a set running Google's operating environment if you need the largest app catalog, Chromecast casting, Google Assistant voice control and consistent Play Store access; opt for a maker's native interface when you want a simpler menu, lower entry price or deeper hardware-specific tunings. If you loved this posting and you would like to obtain additional info with regards to 1xbet login kindly pay a visit to the web-page. Typical midrange devices with Google's software ship with 2–4 GB RAM and quad-core SoCs; flagship boxes and sets push to 4–8 GB plus faster GPUs and dedicated decoders – pick higher memory and a 64-bit SoC for smooth app multitasking and game streaming.
Google's platform advantage: direct access to Google Play (thousands of streaming and utility apps), built-in casting, integrated voice assistant and wider support for third-party peripherals. Expect system updates and security patches more frequently from the platform provider, though manufacturer rollout timing varies by brand. Hardware-dependent capabilities such as Dolby Vision, HDR10+ and Dolby Atmos require both OS support and panel/AV-chip compatibility; verify HDR formats and audio passthrough on the product page before purchase.
Manufacturer interfaces excel at streamlined navigation, manufacturer-specific remote features and sometimes exclusive content or free linear channels. Brands often tune motion handling, local dimming and tuner performance for live TV; this can yield lower input lag and faster channel changes on some models. For lightweight boxes focused on simplicity and broad channel support, consider Roku or proprietary UIs from major panel makers that prioritize stability over customization.
Practical selection checklist: for gamers look for HDMI 2.1, 4K@120Hz support, VRR and ALLM with input lag under 10 ms at 60 Hz; for movie enthusiasts prioritize peak brightness (aim > 1000 nits for HDR highlights), local dimming zones, and hardware passthrough for Atmos and advanced HDR; for cord-cutters verify app availability for local services, tuner support and reliable over-the-air recording. If longevity matters, favor devices with clear update policies and a large app ecosystem rather than closed, low-cost platforms.
Key OS and Platform Differences
Pick a set running Google's platform if you need the broadest app selection, native casting, and frequent Play Services updates; choose a manufacturer or third-party platform for a simpler interface and vendor-specific integrations.
App ecosystems differ by distribution model: Google's platform uses the Play Store with many large-screen ports and third-party sideloading options; Roku, webOS, Tizen and Fire OS use curated stores with stricter certification, which means some niche apps or beta builds may be absent. Before purchase, confirm availability of your subscription services and regional app variants.
Update cadence and lifecycle vary: devices on Google's platform typically receive Play Services and security patches monthly or quarterly from Google plus occasional firmware updates from the maker. Manufacturer platforms often publish irregular firmware schedules. Seek devices that promise at least two years of major updates and three years of security fixes, and verify that commitment in vendor documentation.
Content protection determines true playback quality. For HD/4K DRM playback you need platform support for Widevine L1, PlayReady or vendor-equivalent CDMs plus proper vendor certification for apps like Netflix and Amazon Prime. Check DRM level and confirmed 4K support for each streaming app rather than assuming high resolution is available on all sets.
Casting and screen-mirroring differ: Google's platform includes Chromecast built-in and deep Google Assistant integration; other platforms may offer AirPlay, Miracast or Alexa support. Match the platform to your existing smart-home ecosystem to avoid adapter devices and to enable multiroom or voice routines.
Sideloading and developer access: AOSP-derived builds and Google's platform allow easier sideloading and debugging, useful for advanced users and hobbyist apps. Roku and many manufacturer stores are closed by design; Fire OS permits sideloading but may lack Google Play compatibility. If you plan to run custom apps, prioritize platforms that document developer APIs and permit non-store installs.
Performance depends on both OS efficiency and hardware: low-end sets with 1–2 GB RAM and 8 GB flash will struggle with multiple background apps and 4K decoding. Target devices with 3–4 GB RAM and 16 GB flash for smooth navigation and app updates; for heavy multitasking or local media servers, prefer quad-core SoCs with dedicated video decoders (HEVC/VP9/AV1 where needed).
Remote and search behavior: platforms vary in universal search and voice results aggregation. Google's platform and Roku offer cross-app universal search; some manufacturer shells limit search to preinstalled partners. If quick universal search and voice shortcuts matter, test the remote and search behavior in-store or via online demos.
Checklist before purchase: confirm required apps and their 4K/DRM status; verify vendor update policy and promised support years; check which casting/assistant ecosystem is native; ensure hardware minimums (3–4 GB RAM, 16 GB storage for 4K use); and decide whether you need sideloading or a closed, curated experience.
Core operating system architecture explained
Recommendation: choose a device whose platform uses a modern LTS Linux kernel (>=5.10; 6.1 LTS preferred), strict SELinux enforcement, a vendor HAL/API separation, verified A/B updates with rollback protection, and hardware-backed DRM/key storage.
The kernel provides process scheduling, memory management, device drivers and the graphics/voideo stacks (DRM/KMS). Verify whether GPU and video codecs are supported by mainline drivers or by out-of-tree blobs; mainline drivers and upstreamed kernel backports reduce long-term compatibility issues.
Hardware abstraction layers (HAL) or well-documented vendor APIs must isolate OEM-specific code from the platform framework. A clear HAL boundary lets the platform maintain API stability while vendors supply drivers and hardware features without forcing app rewrites.
Application runtime usually combines a managed runtime (JIT/AOT-capable VM) and native libraries. Look for per-app sandboxing, namespace isolation, seccomp filters and per-app user IDs to reduce privilege escalation risk and to contain misbehaving packages.
Media pipeline architecture: hardware video decoders (H.264/H.265/AV1), proper V4L2/DRM integration, audio routing (ALSA/pipewire/pulse equivalents), HDR metadata handling and HDMI-CEC/HDCP support are implemented at the kernel+middleware boundary. Confirm supported codec profiles, container formats and DRM levels (Widevine L1 / PlayReady equivalents) for streaming quality and protected playback.
Update and signing model matters for reliability: A/B (seamless) updates with delta transfers, signed images and verified boot reduce brick risk and allow safe rollbacks. Check the vendor’s published update cadence and whether security patches are backported into the shipped kernel.
Security hardware: secure boot chain, Trusted Execution Environment (TEE) or secure element for key storage, and runtime attestation improve content protection and credential safety. Ensure attestation and key escrow policies are documented and controllable by the end user.
Compositor and input stack design affect responsiveness and latency. Prefer compositors that use hardware overlays, vsync-driven composition and GPU-accelerated rendering; this lowers frame drops, reduces input lag for remotes/game controllers and lowers CPU load.
Resource management: cgroups v2, a modern scheduler, and a robust low-memory handling policy determine multitasking behavior. For comfortable multitasking and background app retention choose devices with at least 2–3 GB RAM and an OS that exposes predictable background limits.
Telemetry, preinstalled services and update control should be explicit: platforms that separate vendor apps from core system services and that permit disabling data collection offer clearer privacy and easier troubleshooting. Verify available settings and any mandatory cloud services before purchase.